Redistricting
Representatives are allocated by population. The higher the state’s population, the more representatives they have.
The total number of representatives has been fixed for a while. This means that if one state gets more representatives, some other state gets fewer.
Not only do representatives determine the make up of the House, they also determine the make up of the electorial collage.
Thus, the number of representatives a state has is critical in determining political outcomes.
One of the issues currently being debated is a new census before the 2028 election. There are indications that some states, such as California, are overrepresented because the census counted criminal illegal aliens. Look into the 3/5s clause in the Constitution for why this is an issue.
After every census, the states can redistrict based on the new census numbers.
In 1965, Congress passed the Voting Rights Act of 1965. This act sets new rules for how the representatives should be chosen by the many states.
Unfortunately, this act is likely at odds with the Constitution. In particular the Fourteenth Amendment. Any law that Congress passes that is contrary to the Constitution is void. Unfortunately, it takes a case reaching the Supreme Court and the Supreme Court agreeing the law is contrary to the Constitution for the law to be struck down.
Of course, this hasn’t stopped rogue, agenda-driven, inferior court judges from pretending that Congress can pass laws restricting the powers of the Article II executive.
The question then becomes, “How do you create districts for a state that are representative of the people of the state?”
Generally the districts of a state are created to control the outcome of elections.
Here is part of the 2011 congressional districts of Maryland:
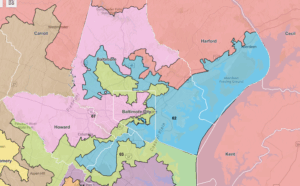
If you look at Congressional District 01 in orange, you can see that it has many counties within it. But more importantly, it extends into Baltimore County. The same with District 02. Most of the military of the Aberdeen Proving Grounds and Edgewood Area are in District 02. But I also include a part of Baltimore City and Howard County.
I’m sure you would not be surprised to learn that the very high concentration of PoC voting Democrat causes Districts 01 and 02 to be Democrat districts.
The current congressional districts follow the county borders.
The way this worked was that everybody knows that Baltimore is a huge Democrat stronghold. It is so huge that they can dilute it with Republicans and still come out for the Democrats.
By using the Democrat voters of Baltimore in districts 1, 2, 3, and 7 they made 4 of the 8 districts +Democrat. District 4 is using the Democrat voters of Montgomery County to overwhelm the Republican voters of the rest of the district. Districts 5, 6, and 8 are Democrat strongholds; they don’t need any help from the city.
This districting leaves Republicans of Maryland without representation in Congress.
In Louisiana v. Callais the Supreme Court is hearing a case challenging the VRA on Constitutional grounds.
In Robinson v. Ardoin in 2023, a district court found that Louisiana had violated the Voting Rights Act of 1965. The inferior court ordered the state to create an additional majority-black district to avoid “vote dilution.”
This court order resulted in Louisiana’s SB8. The sponsor of SB8 said “We all know why we’re here. We were ordered to draw a new Black district, and that’s what I’ve done”.
That new district stretches 250 miles from the Shreveport in the northwest to Baton Rouge in southeast Lousiiana.
All to create another black district. When we say black district, what is really meant is “Democrat district.”
Well the Supreme Court got the case and decided to punt. Thomas was unhappy with that and told the world how unhappy he was.
This case was argued on March 24th in the 2024 term. Instead of issuing an opinion before the end of the term, the Court instead put the case back on the calendar for reargument.
It appears that the Court wants to be briefed on specific aspects of the case.
Conclusion
This case is outside my knowledge base. In trying to understand the question presented, I’m lost. And that is just one page. Thank goodness Thomas writes in English that I can understand.
This is just another case clawing back the rights of The People after years of reverse descrimination.